BSidesPDX CTF 2018
Links
Introduction
Over the weekend of October 26th and 27st I ran the BSidesPDX CTF for the third year with an amazing team consisting of fdcarl, aagallag, dade, and arinerron with infrastructure supported by Mozilla. We decided to run all of the challenges in Docker containers in Amazon Web Services (AWS) k8s again this year using the deployment framework from our 2017 CTF.
This post will detail some of our decisions, the results and improvement areas.
Challenges
For the 2018 CTF we had 12 challenges across 4 domains
-
Web Exploitation
-
Binary exploitation / Reverse Engineering
-
OSINT
-
Forensics
OSINT and Forensics challenges were new to BSidesPDX this year. During the post mortem of BSidesPDX 2017, it was mentioned that our CTF was only offensive security focused and had no defense challenges. Given I am a huge proponent for cross training, I decided to enlist arinerron to write 3 forensics challenges for us.
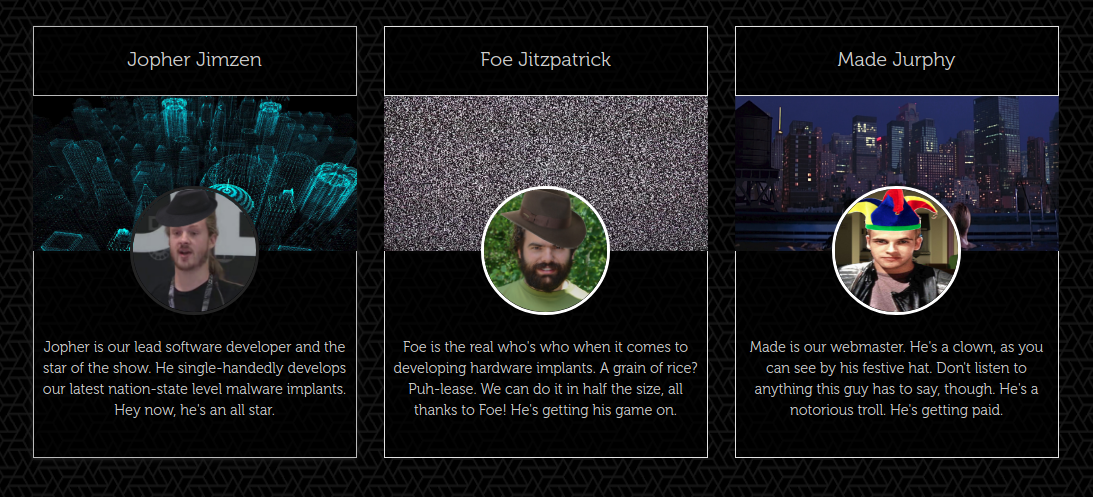
OSINT was also added as dade has a passion for it and given we had added the OSINT CTF from Trace Labs (a writeup from them is available here) we felt it necessary to include some CTF challenges in this category. The OSINT CTF made use of LinkedIn, GitHub and a custom website.
fdcarl would up writing the web challenges and aagallag the two binary exploitation challenges.
Our concepts at a higher level are available here and all of the source code for them is located at their respective category and level on the repo here. All challenges have solutions and can be deployed with docker-compose.
The challenges were meant to target beginner/intermediate players and I feel did a sufficient job of that. We had people in the event room that had never played a CTF before solving challenges and catting flags (in fact, 8 people came up on stage during closing ceremonies to collect a beer mug for their accomplishment)
Infrastructure
Infrastructure was once again hosted by Mozilla with Daniel Hartnell doing all of our orchestration. A shout out to Jeff Bryner and Andrew Krug are necessary as well as they helped provide the monetary resources and getting me in touch with Daniel.
We once again used our 2017 framework to deploy docker containers to a kubernetes environment that utilized
- Kubernetes in AWS via Amazon EKS
- Network policies to restrict pod network access
- kube2iam to provide restricted IAM roles to pods
- Disabled ServiceAccount token mount inside pods
- RBAC enabled
Scoreboard
Having used it in the past, going with CTFd was a no brainier. It is easy to deploy and administer. We hosted our scoreboard at BSidesPDXCTF.party. We also did this for 2017 and this paragraph was copy/pasted!
Results
This year we had
89 teams register (up from 62 in 2017)
26 teams solved challenges (double than last year which had 13 teams ! ! !)
Most solved: Leaky Secrets has the most solves with 19 solves
Least solved: Hidden with 1 solve
Solved breakdown
-
19 Leaky Secrets
-
12 Death by 1000 Curls
-
12 Leaky Security
-
8 Leaky Projects
-
3 secureshell
-
3 Trollsec
-
3 mic
-
3 capture
-
2 goxor
-
2 Dodona
-
2 pwnclub
-
1 hidden
People liked solving the OSINT challenges!
It is also worth stating that this year EVERY challenge was solved at least once! The 2017 CTF had some overly difficult challenges that were never solved and we reevaluated the difficulty of challenges for this event.
Final Scoreboard:
Place Team Score
1 pixel 1500
2 broken 1100
3 sectribe 1000
4 fadec0d3 800
5 Zer0C001 700
6 thisshitistemp 700
7 w 700
8 Did you just assume my endianness? 600
9 Chip's Challenge was a Warning 600
10 Reenigneesrever 600
11 NotSoBrightmail 500
12 meow_meow 400
13 l4y3r-8-f41lur3 300
14 Qult of the Quantum Qows 300
15 Josh Gesler 300
16 MrStealYourFlagz 300
17 HP Inc. 300
18 Threat Actor's Guild Local #503 300
19 themask 200
20 SGksIEknbSBFcmljISAK 200
21 illusorycake 200
22 vans 200
23 GNU-e-Ducks 200
24 mdalin 100
25 The New Guy 100
26 Russian Election Manipulators 100
What To do Better / Different
Live scoreboard: We did not even think of having a live pew pew scoreboard during the CTF in the event room…. our mistake. we will be better.
OSINT 200 had the most solves of the entire event with 19 teams solving it. We are thinking of using Dynamic Value Challenge next year to reduce the amount of points a challenge has if it is solved frequently.
Get Involved!
If you want to help us run BSidesPDX CTF in anyway please reach out to me! We are eager to get some people stoked on writing challenges to make 2019 even better. The idea behind a base reference implementation is that the challenge creation comes to the foreground much easier and can be focused on without worrying about much else!
Thanks
I want to extend another huge thanks to